Why SekuirTek
What differentiates us.
Technology decisions should protect the business, support compliance, and drive strategy — not just keep systems running. We bring executive-level oversight to your security and operations.
Why Choose Us
Security That Speaks the Language of Risk
We don’t just deploy tools, we design governance‑driven security programs that translate technical controls into business outcomes your leadership can understand and act on. Every service aligns with our four core pillars, ensuring your organization receives structured, compliant, and measurable protection.
Whether you need stronger governance, clearer executive‑level insights, hardened security, or safe AI adoption, we provide a framework that delivers clarity for your leaders, evidence for your auditors, and continuous protection for your operations.
✔ Governance‑First IT
Governance‑aligned methodology built on frameworks like NIST, CIS, HIPAA, and CMMC, ensuring your policies, procedures, and controls are defensible and audit‑ready.
✔ Executive Risk Mitigation
Business‑focused reporting and dashboards your board, executives, and auditors can actually understand, including quantified risk, compliance status, and trend analysis.
✔ Cloud Workspace Management
Deep expertise in security‑hardened Microsoft 365 and Google Workspace environments, including Zero Trust identity, conditional access, DLP, and advanced threat protection.
✔ AI Strategy & Governance
Guidance for safe AI adoption, ensuring tools like Microsoft Copilot enhance productivity without introducing data leakage, compliance violations, or unmanaged risk.
⭐ Flexible Leadership & Support
- Fractional CIO / CISO services for governance and strategic oversight
- Flexible engagement models designed to fit your size and budget
- Proven incident response capabilities with rapid containment and support
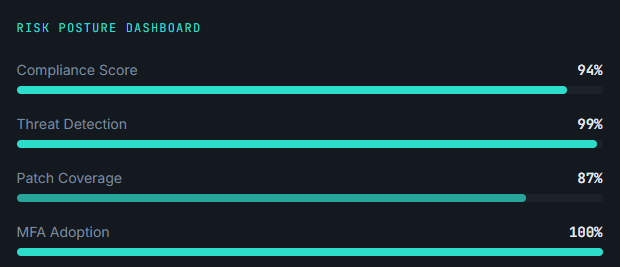
📊 Risk Posture Dashboard
Our governance‑driven approach isn’t theoretical — it produces real, measurable gains across compliance, security, and cloud readiness.
94% Compliance Score
Achieved through governance frameworks, policy development, and structured controls.
99% Threat Detection
Enabled by hardened Microsoft 365 environments and continuous risk monitoring.
87% Patch Coverage
Increased through disciplined change management and ongoing oversight.
100% MFA Adoption
A cornerstone of our Zero‑Trust identity strategy for both Microsoft 365 and Google Workspace.
These results reflect the combined impact of our four pillars working together to strengthen your environment.
Your Trusted Security Partner
We don't just provide services, we become an extension of your team, committed to your organization's security success.
Industry Expertise
Our team brings decades of combined experience in cybersecurity, compliance, and IT risk management across diverse industries.
Rapid Response
When security incidents occur, every second counts. Our rapid response team is ready to act immediately to minimize damage.
Proven Results
We've helped organizations of all sizes achieve compliance, reduce risk, and strengthen their security posture measurably.
Dedicated Support
Get personalized attention with a dedicated security advisor who understands your unique business needs and challenges.
Reliability
Consistent performance and uptime ensure efficient, reliable service with minimal interruptions and quick response times.
Performance
Speed and efficiency ensure tasks are completed quickly and resources are used optimally, enhancing productivity and satisfaction.
Scalability
Growth capability is a system's ability to scale and adapt, meeting increasing demands and evolving needs for long-term success.
What You Get
At a Glance
We don't just deploy tools, we build governance programs that translate technical controls into business outcomes. Your leadership team gets clarity, your auditors get evidence, and your operations stay protected.
- Governance‑First methodology aligned to NIST CSF, CMMC, and CIS Controls
- Executive‑level reporting your board and auditors will understand
- Security‑hardened Microsoft 365 configurations with Zero Trust
- Dedicated virtual CISO services for strategic risk oversight
- Flat‑rate managed services with predictable monthly costs
- Proven incident response with rapid containment SLA